Secure your code, supply chain and runtime instantly
Equip your engineers with the only AppSec tool they need to ship safely.
Continuous SAST, SCA, Secrets, IaC and DAST scans, all in one place.
Compliance-ready AppSec baked into your workflow
Make application security a by-product of your SDLC,
not a flow-stopper for your engineers.
AI Agent
Enforce secure GenAI code on every prompt
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Editor
Scan and auto-fix security and quality issues instantly
Review
- Secret scanning
- Insecure dependencies (SCA)
- SAST
- Code quality violations
- Complex code
- Error-prone code
- Unused code

Git Repo
Catch risky and untested code before merging
Review
- Secret scanning
- Infrastructure-as-code (IAC)
- SAST
- Insecure dependencies (SCA)
- Code quality violations
- Complex code
- Error-prone code
- Unused code
- Code duplications
- Untested code (unit test coverage)
- AI policy violations

Production
Scan your API endpoints and apps at runtime
Review
- Pen-testing
- DAST


"Codacy makes sure that we do security testing on code automatically so the developer doesn't have to worry about it."

Application Security for busy engineering leaders
Stop choosing between shipping fast and staying secure. Codacy automates AppSec guardrails across your entire SDLC, so your engineers can focus on building while Codacy handles the risk.
Daily CVE and malicious package re-scans
Protect new and old code against insecure libraries and malicious packages, with daily CVE database updates.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Source code security
Detect security violations like hardcoded secrets, broken access control and injection threats before they make it to production.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls
Catch hardcoded secrets and credentials pre-commit
Identify exposure risks like leaked credentials, unprotected tokens, and service keys before they enter version control.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls
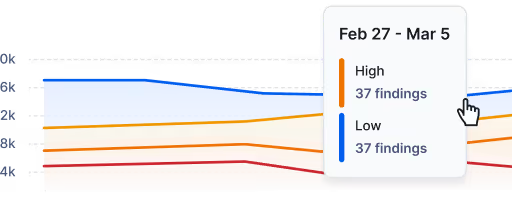
Audit-ready reports
Track your security & compliance posture in real-time, including SLA due dates and exportable SBOM reports.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Source code security
Detect cloud misconfigrations excessive permissions and open network ports before they provision live infrastructure.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Runtime testing
Dynamically test your apps and API endpoints and find vulnerabilities before hackers can exploit them.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

AI Guardrails built into every agent and IDE
Enforce secure coding practices and vulnerability guardrails for all AI-generated code suggestions in real-time.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Exportable supply chain evidence
Export comprehensive dependency lists and license compliance reports to secure your software supply chain.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Centralized AI Coding Policies
Enforce AI Coding Policies to catch risks like unapproved AI models and vulnerable libraries from outdated training data.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

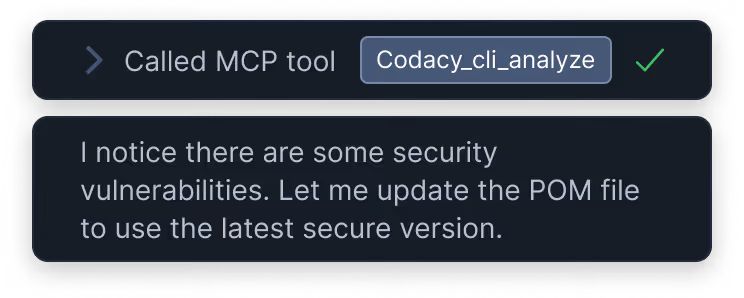
Built for agentic workflows
Turn your security policies into automated guardrails for every AI coding agent used by your devs. Open review-ready Pull Requests on first try.
Get the security context your agent is missing
Codacy Guardrails brings reliable, deterministic code analysis inside your agentic workflow, making your coding agents follow the rules you define, consistently.
Give your agent the context it needs to auto-repair new and old code on the fly.
Get secure AI code on every prompt
Codacy Guardrails silently scans every line of AI code against your security policies, whle it's being generated. Let your agent auto-fix its own issues, before you even see the code.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Patch legacy vulnerabilities without leaving the chat panel
Turn Codacy’s scan results into actionable context for your AI agents. Empower them to auto-remediate every identified vulnerability across your legacy codebase with verified precision.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Adjust your policies and get security reports
Set your AI Guardrails to match your organization's security policies and apply them across agents and IDEs. Generate comprehensive security reports across teams and projects.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Loved by engineers
Codacy has changed the way engineering teams ship secure, high-quality applications without sacrificing speed.
Lorem ipsum
Enforce secure GenAI code on every prompt
"A Game-Changer for Code Quality
and Team Productivity”
Sarang K.
Technical Project Manager
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Great tool for detecting code issues,
code coverage, code duplication and
code complexity"
Miroslav B.
Senior Card System Architect
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Great tool to ensure your quality
standards"
Vinicius P.
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"A company that understands
developers"
Verified User in Education Management
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Pushing our quality higher as they
continually improve their platform
and customer success"
Michael G.
Principal Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Helps maintain high standards for
our code."
Chiesa B.
Back End Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Excellent code coverage tool with
great GitHub Integration"
Misagh M.
Software Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"A great tool to review your code"
Matteo B.
Software Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Easy to integrate hard to give up!"
Mustafa O.
Mobile Development Lead
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Boost your team code static
analysis, quality and more"
Madalin V.
Senior Software Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls


Start Pen-testing
Penetration testing is now available for Codacy Business tier customers. Get a discount on Bullet proof cyber security pen testing services and see the results on the Codacy Security dashboard.

