The safety layer for AI-accelerated coding
Coding agents make devs ship more risky code faster.
Don't leave a single line of AI code unchecked.
One AI Policy for All Your Projects
A dedicated ruleset designed to prevent risks and vulnerabilities that are inherent to AI code from entering production.
Unapproved model calls
Prevent shipping code that contains API calls to unapproved large language models
- Secure MCP Servers & Libraries
- Prevent Data Leakage Risk
- Instant Policy Enforcement

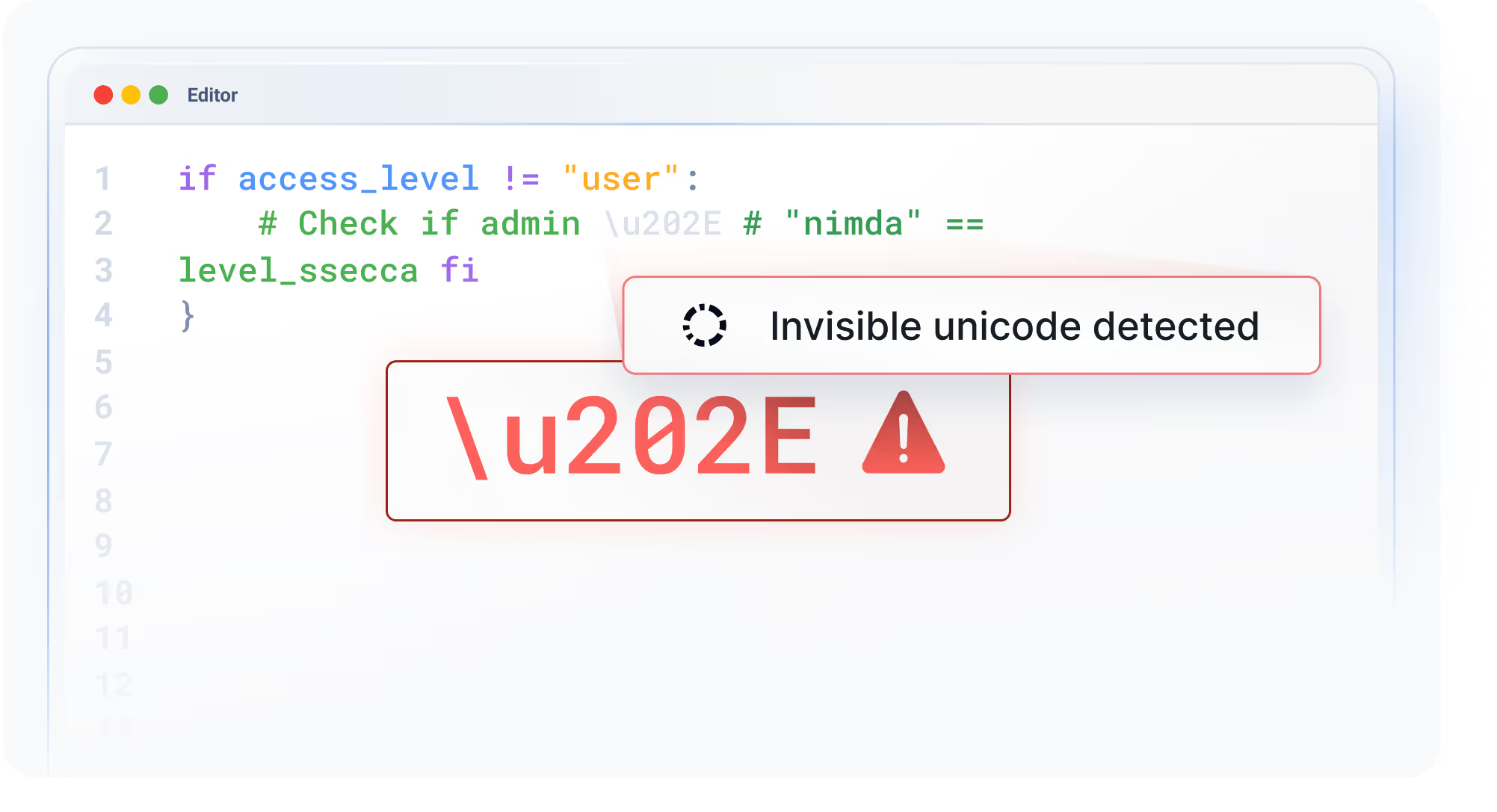
AI Safety
Catch AI-specific risks like invisible unicode injections before they hit production
- Catch invisible unicode before it can be executed
- Avoid security flaws replicated from training data
- Prevent SQL injection caused by unsanitized user input

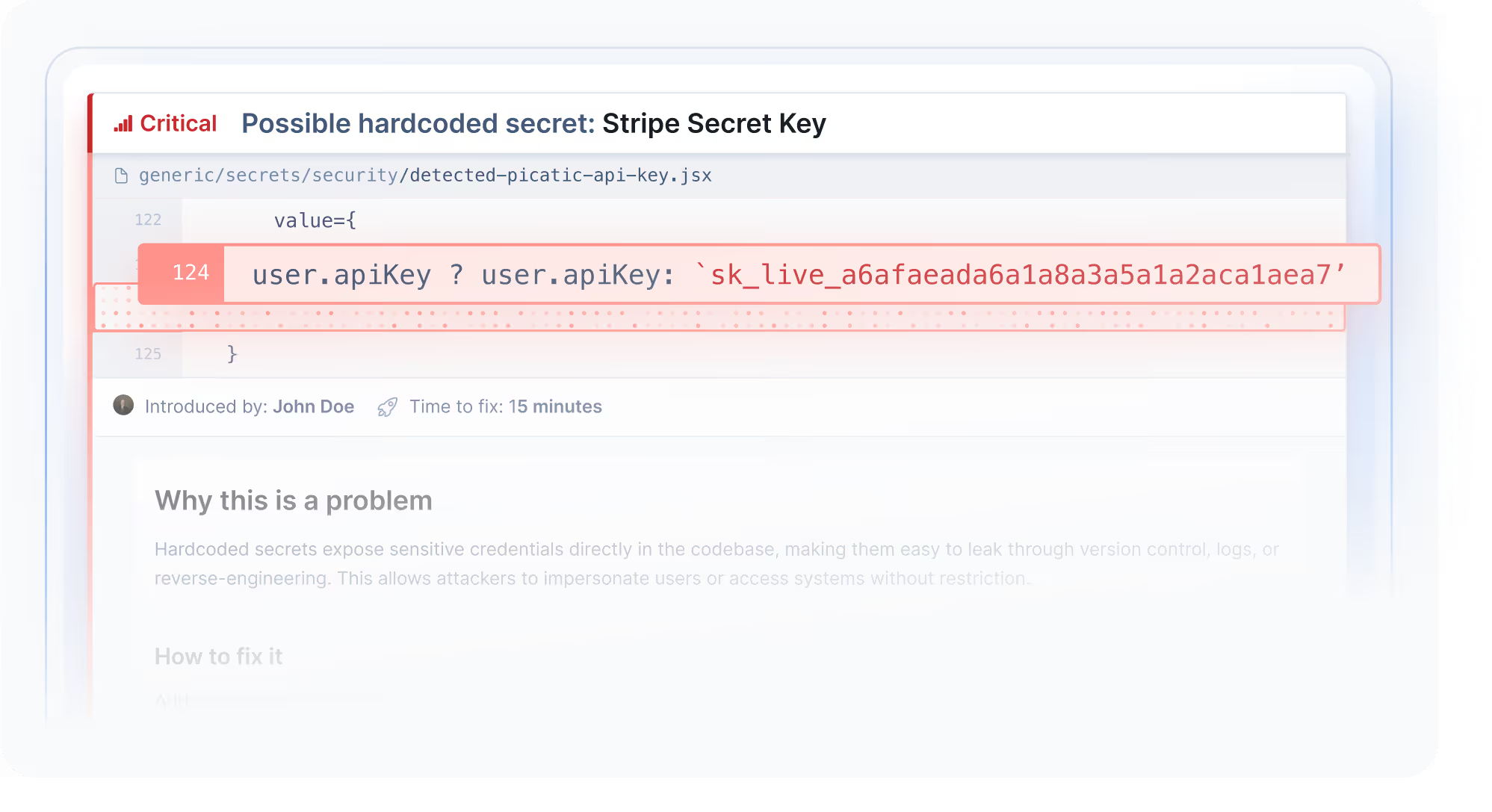
Hardcoded Secrets
Detect hardcoded secrets and API tokens before they reach Git and production
- Real-time Guardrails for AI coding agents
- Pre-commit secret detection
- Prevent leaking credentials

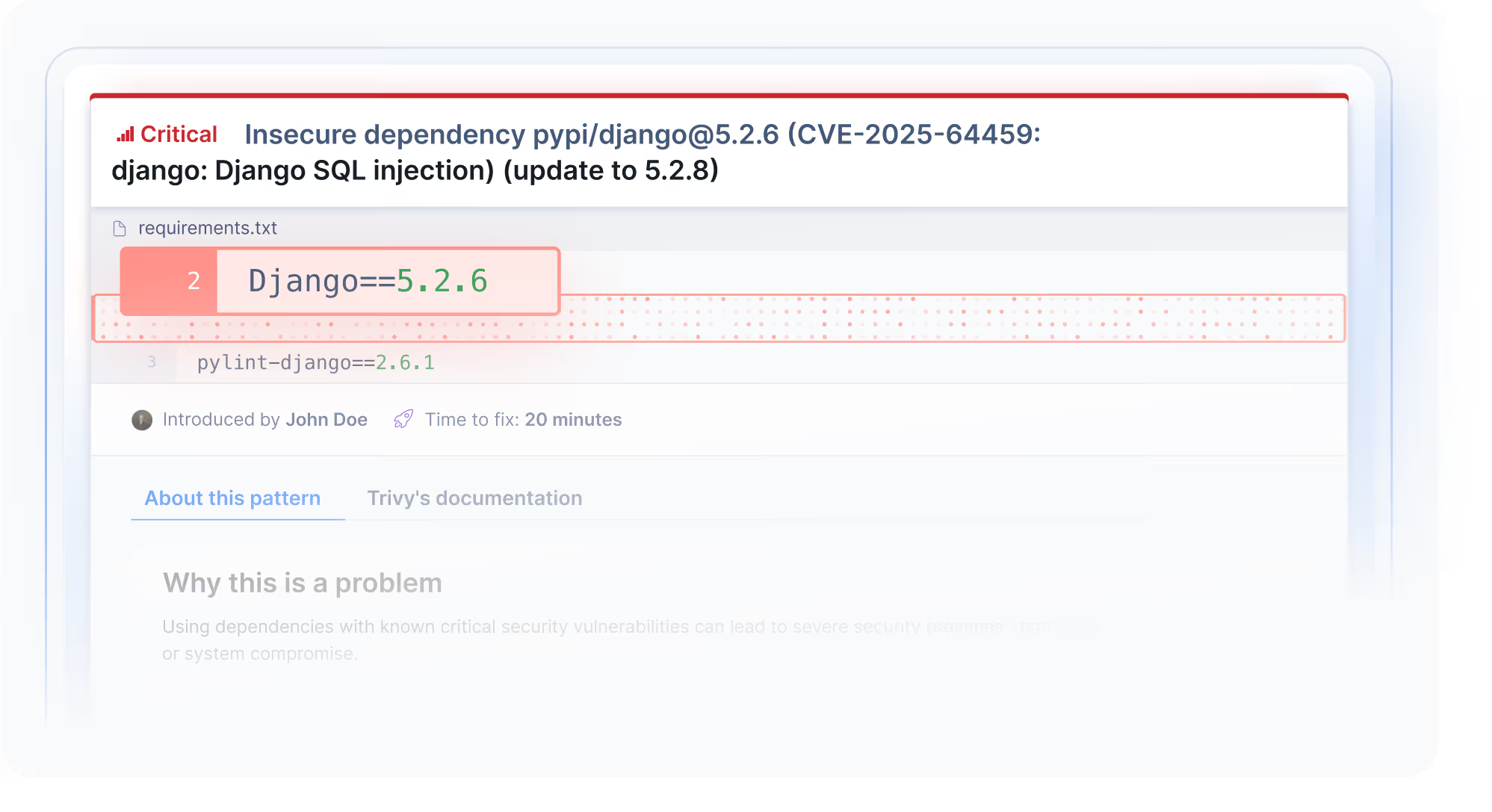
Vulnerabilities
Catch insecure dependencies introduced by AI coding agents
- Enforce secure, up-to-date library versions
- Daily CVE database updates
- Supply chain analysis across the codebase


"Codacy makes sure that we do security testing on code automatically so the developer doesn't have to care about it."

A unified checklist to manage your AI risk score
Code scanning is only part of the equation. Enforce all essential merge controls to truly protect your codebase from risky AI code contributions.
AI Policy applied
Your AI Policy is defined and enabled across all projects.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Protected pull requests
Your Pull Requests have strict branch protection enabled
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Coverage enabled
Your unit test results are successfully configured and reported to Codacy
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Vulnerability scans
Your projects are continuously scanned daily for new CVE risks
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Enforced gates
Your merge gates are defined and enabled across all project
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Apps scanned (DAST)
Your web apps and endpoints are configured for App Scanning
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls


Ready to dive in?
Try the AI Risk Hub today

Codacy Guardrails
The first comprehensive solution that secures your development process against both traditional and AI-generated security vulnerabilities.
Keep your favorite AI coding agent.
Shift left completed. Once and for all
Guardrails is not yet another AI model for code reviews. Instead, it pairs trusted static analysis methods with the power of your existing AI coding assistant, delivering unmatched speed and convenience – without leaving a trail of destruction.
Install Codacy IDE extension
Guardrails runs inside VS Code, Cursor, and Windsurf, seamlessly embedded in your existing AI coding workflow.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Write code with your AI agent
Every line of AI-generated code is silently scanned for security and quality flaws, and auto-fixed – all before even printed.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

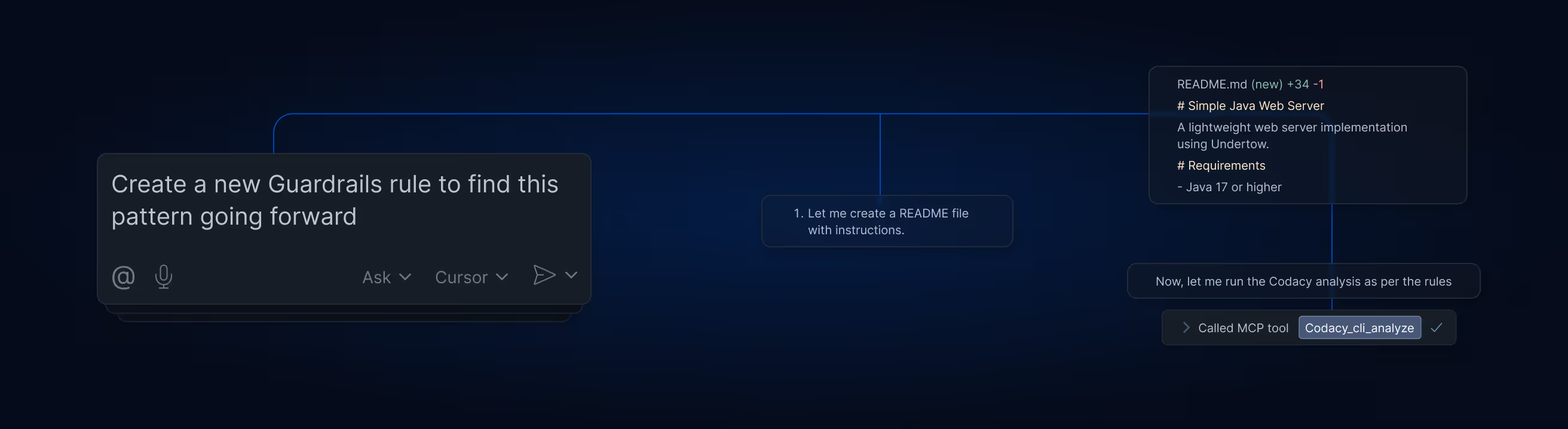
Tweak the rules to your vibe
Set the default scan rules to match the standards of your codebase – and apply them across all IDEs in your team.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

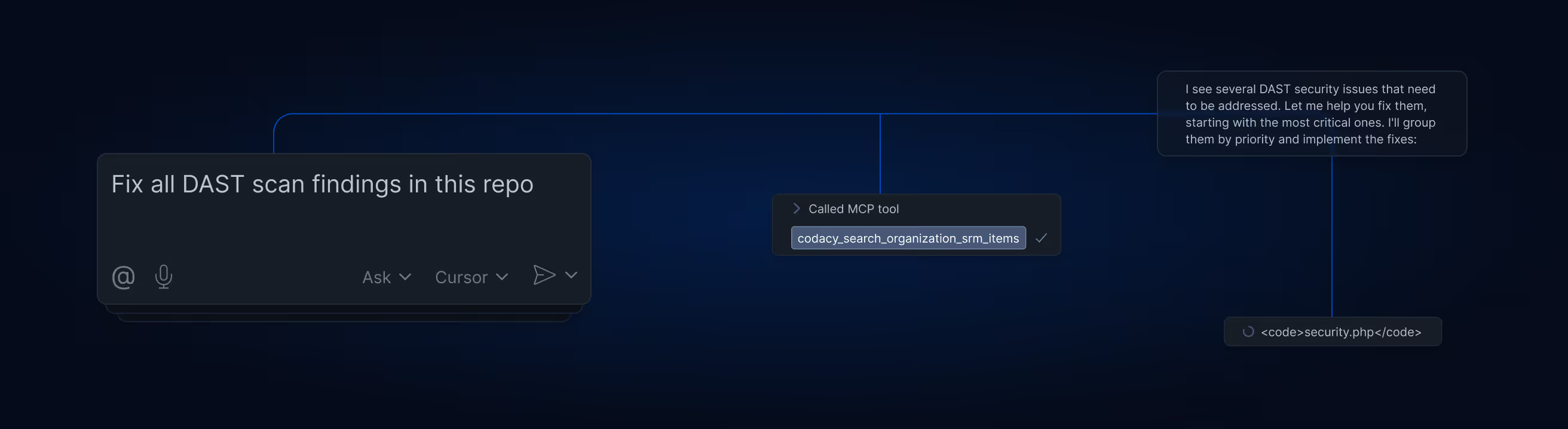
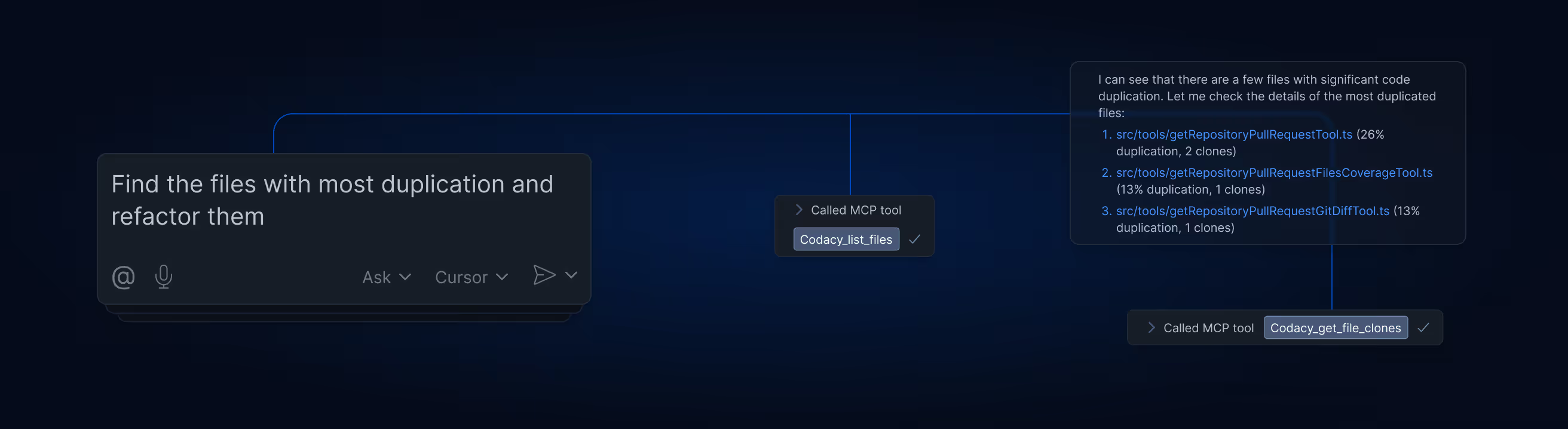
One source of truth. Limitless possibilities
Guardrails is more than scanning AI code in real time. Using MCP technology, we created a brand new way of interacting with all scan results in the Codacy cloud platform, and letting your AI assistant fix them in bulk – without ever leaving the chat panel.
Loved by engineers
Codacy has changed the way engineering teams ship secure, high-quality applications without sacrificing speed.
Lorem ipsum
Enforce secure GenAI code on every prompt
"A Game-Changer for Code Quality
and Team Productivity”
Sarang K.
Technical Project Manager
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Great tool for detecting code issues,
code coverage, code duplication and
code complexity"
Miroslav B.
Senior Card System Architect
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Great tool to ensure your quality
standards"
Vinicius P.
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"A company that understands
developers"
Verified User in Education Management
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Pushing our quality higher as they
continually improve their platform
and customer success"
Michael G.
Principal Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Helps maintain high standards for
our code."
Chiesa B.
Back End Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Excellent code coverage tool with
great GitHub Integration"
Misagh M.
Software Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"A great tool to review your code"
Matteo B.
Software Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Easy to integrate hard to give up!"
Mustafa O.
Mobile Development Lead
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Lorem ipsum
Enforce secure GenAI code on every prompt
"Boost your team code static
analysis, quality and more"
Madalin V.
Senior Software Engineer
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls
