Codacy is the Best Snyk Alternative
The Snyk alternative that goes further: secure code, supply chain, code quality, and AI code risk management unified. All without breaking your budget.
Trusted by 15,000+ organizations and 200,000+ developers worldwide
Why engineering teams choose Codacy as a Snyk Alternative
Seamless shift left security built for dev teams
Codacy helps devs fix vulns as soon as they appear in the IDE or Pull Request, avoiding the reactive, time-consuming workflow of legacy tools like Snyk.

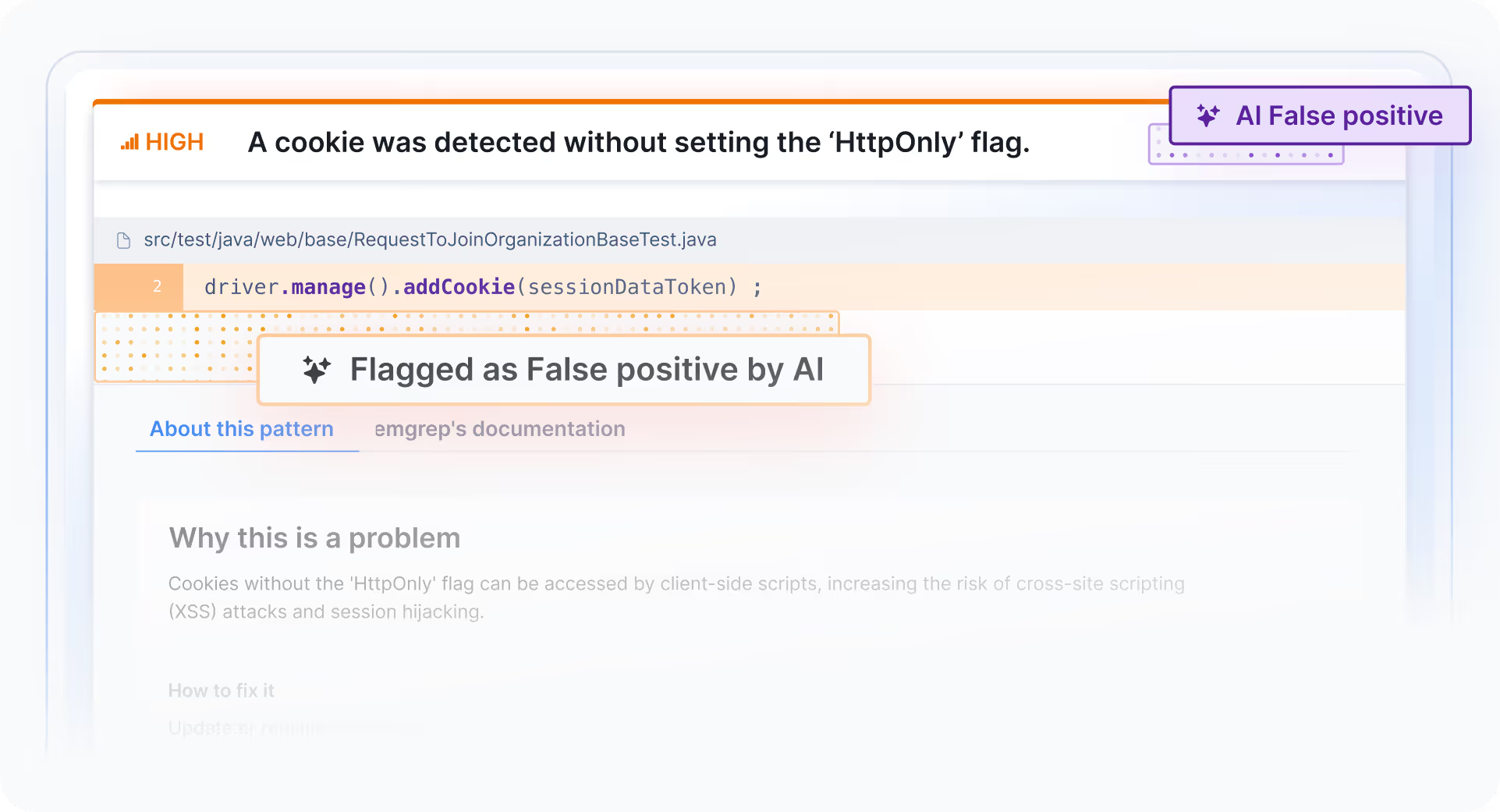
Cut through the noise
Code review fatigue slows down releases and exposes code to unchecked security risks. Codacy flags false positives automatically so devs don’t need to find the needle in the haystack.

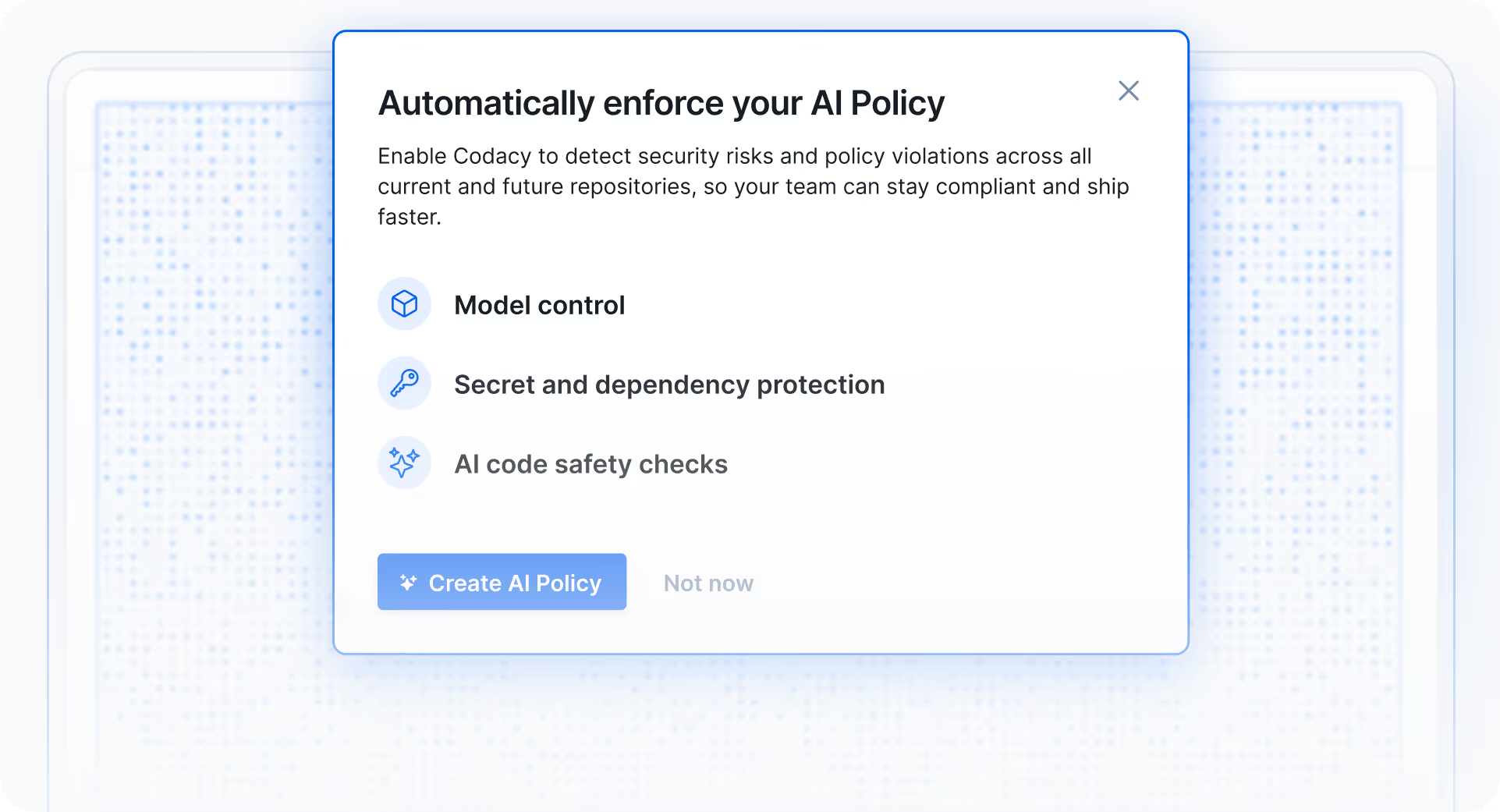
Built for AI-accelerated software development
Codacy protects your entire codebase against new AI-specific security risks, by enforcing AI coding policies across all your projects with a single click.

Enterprise-grade AppSec without enterprise overhead
Codacy Business customers switching from Snyk cut their tooling cost by 67%. Predictable, user-based pricing without hidden fees.

Quality code is secure code
True AppSec starts with healthy coding practices that everyone follows. Define org-wide quality, coverage and security standards, and embed them across the entire workflow.


"Codacy is now a foundation of our development process. For the past two years, we’ve used it to block the introduction of new critical security issues, effectively closing the gate on risk while we work through our legacy backlog. It’s given us the guardrails we need, especially as AI-generated code increases our volume."
Ronen Y. Director of Developer Experience at LSports
Zero
new critical security issues introduced over two years
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

800
core repositories standardized under unified coding policies
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

10x
increase in unit test coverage across projects
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls


Snyk vs Codacy comparison
Codacy delivers end-to-end AppSec. No servers or build steps needed.
When to choose Codacy over Snyk
Teams demanding predictable ROI
For organizations tired of the "security tax" and complex, module-based pricing. Unlike Snyk’s costs which can spike based on scan frequency, Codacy offers a transparent, flat-rate structure with unlimited scans and a predictable price that scales with your team, not your scan volume.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

DevEx-obsessed engineering cultures
For teams that want security integrated into the developer flow, not treated as a separate bottleneck. While Snyk often creates "security noise," Codacy provides actionable insights directly in the IDE and the PR, helping developers fix vulnerabilities instantly without ever leaving their preferred environment.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Rapid growth with zero-config needs
For companies that need enterprise-grade security gates without the infrastructure overhead. Instead of Snyk’s complex pipeline and CLI configurations, Codacy’s "pipeline-less" approach allows for one-click setup across hundreds of repos, eliminating the need for dedicated maintenance resources.
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

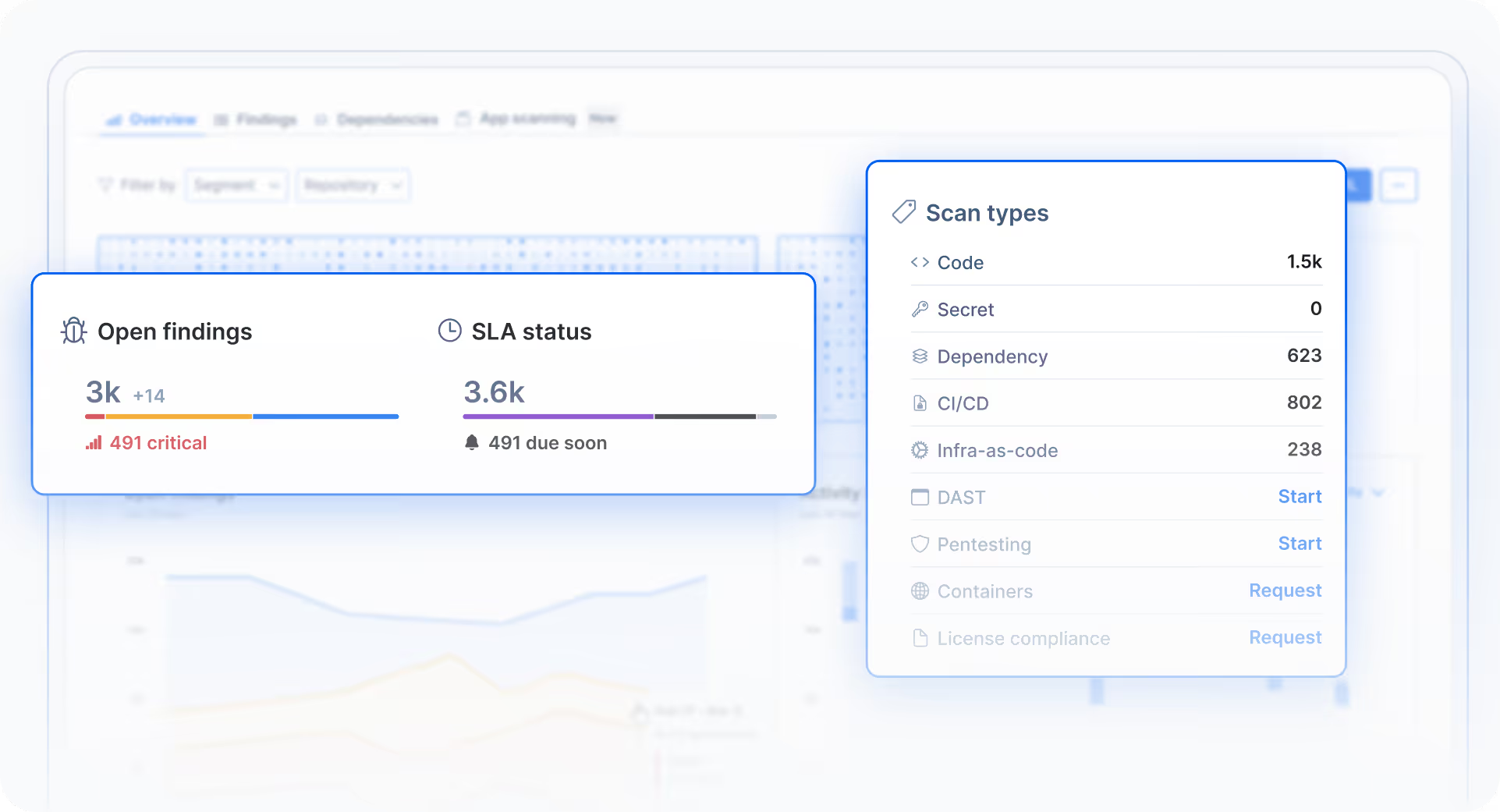
End-to-End protection, ready for AI Coding
Today's development teams face complex challenges that traditional tools can't solve.
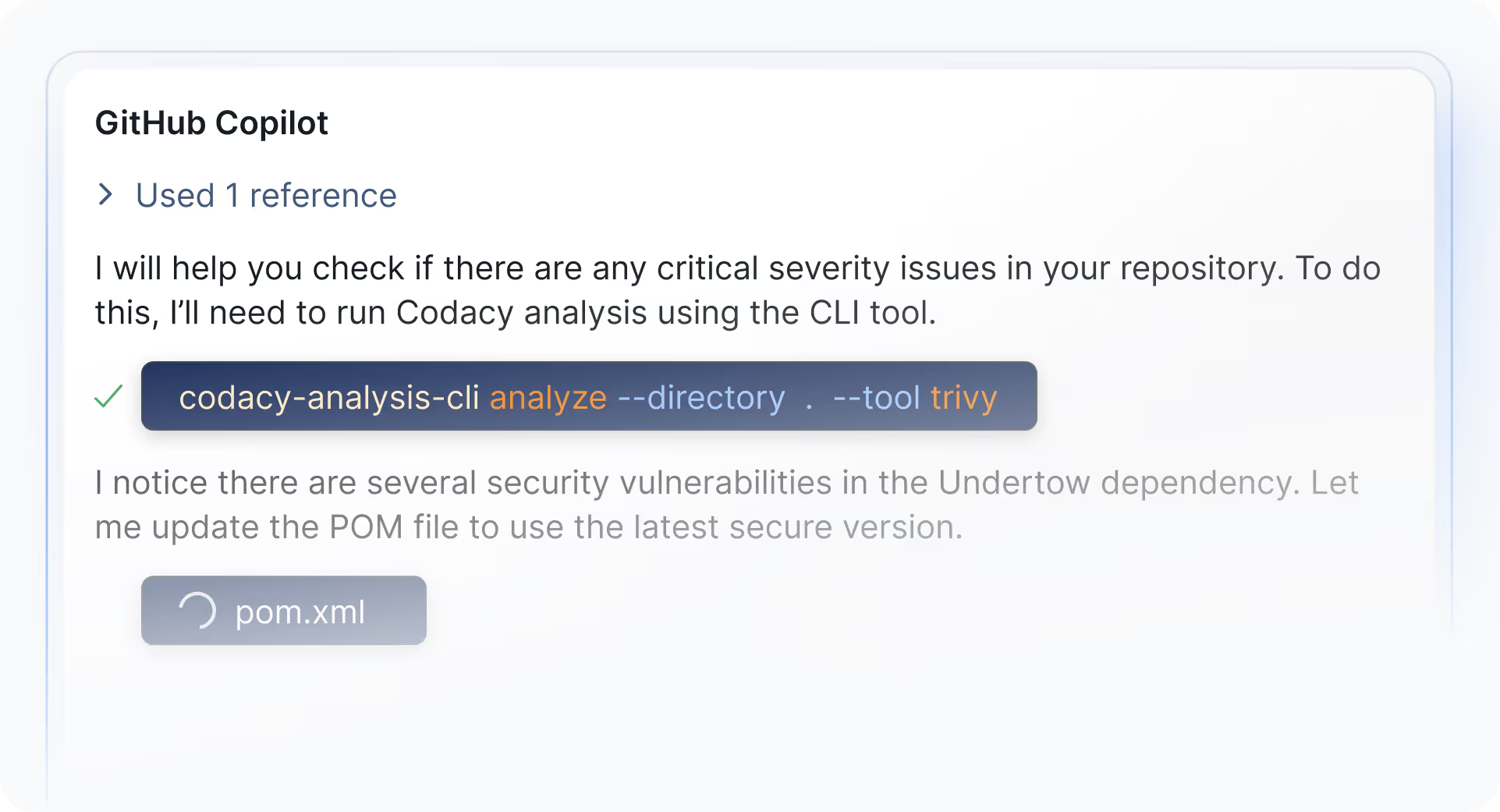
AI Agent
Enforce secure GenAI code on every prompt
Review
- Secret scanning
- Insecure dependencies (SCA)
- AI policy violations
- SQL Injections
- SAST
- Unapproved model calls

Editor
Scan and auto-fix security and quality issues instantly
Review
- Secret scanning
- Insecure dependencies (SCA)
- SAST
- Code quality violations
- Complex code
- Error-prone code
- Unused code

Git Repo
Catch risky and untested code before merging
Review
- Secret scanning
- Infrastructure-as-code (IAC)
- SAST
- Insecure dependencies (SCA)
- Code quality violations
- Complex code
- Error-prone code
- Unused code
- Code duplications
- Untested code (unit test coverage)
- AI policy violations

Production
Scan your API endpoints and apps at runtime
Review
- Pen-testing
- DAST


Ready to make the switch?


Built for and loved by devs
Frequently asked questions
Unlike Snyk pricing, which often involves complex modules and costs that spike based on scan frequency, Codacy offers a transparent, flat-rate structure. We provide a predictable alternative to the high Snyk cost that scales with your team size, not your scan activity, so you aren't penalized for scanning more often.
Yes. While the Snyk tool ecosystem is often fragmented into separate products, Codacy provides a unified platform for SAST, SCA, Secret Scanning, IaC, Malware detection, DAST and Pentesting, embedded in your developer workflow.
A common Snyk review complaint is the high volume of false positives. While Snyk SAST can overwhelm developers with noise, Codacy is built for developer experience. We filter the noise to provide actionable insights directly in the IDE and PR, helping your team fix real threats instantly without the alert fatigue.
Yes. Codacy provides robust Software Composition Analysis (SCA) to identify vulnerable open-source libraries and license risks, but with significantly less friction. While Snyk SCA often bombards developers with alerts for safe dependencies, Codacy filters out the noise so you only focus on what truly matters. Additionally, Codacy includes built-in malware detection to catch malicious packages, a critical layer of supply chain security that Snyk SCA doesn't provide.
Migrating is simple and significantly reduces your DevOps overhead. While a Snyk's setup often requires manual CLI configurations and ongoing pipeline maintenance across every repository, Codacy uses a "pipeline-less" approach. By connecting directly to your Git provider, you can automate security gates across hundreds of repos in minutes without writing a single line of CI/CD code.
Yes. While some tools treat security as a separate gate, Codacy integrates results directly into the IDE and the PR. This ensures that security is a natural part of the developer workflow, making it much more intuitive than a standard Snyk vulnerability scanning setup.
Yes. A common Snyk review complaint is that high-touch technical support is often gated behind a $20k+ minimum spend. At Codacy, we believe security is a partnership. Every customer gets access to expert support and guidance to help them scale, regardless of whether they are a growing startup or a large enterprise.
Engineering teams switch to Codacy for three main reasons: predictable ROI, superior developer experience, and setup simplicity. Unlike the "security tax" and fluctuating Snyk cost, Codacy offers a flat-rate structure with unlimited scans. While the Snyk tool can create workflow bottlenecks and "security noise," Codacy delivers actionable insights directly in the IDE and PR. Finally, Codacy’s "pipeline-less," zero-config setup allows you to secure hundreds of repos instantly without complex CI/CD steps and pipeline maintenance required by Snyk security products.
Yes. You can start with a free 14-day trial of the Codacy Team plan with up to 5 repositories. Organizations with 30+ developers can also opt for an extended 4-week proof-of-value (POV) of the Codacy Business plan, including dedicated expert guidance and configuration support.
Ready to make the switch?